Use OSV-Scanner to find existing vulnerabilities affecting your project's dependencies. OSV-Scanner provides an officially supported frontend to the OSV database and CLI interface to OSV-Scalibr that connects a project’s list of dependencies with the vulnerabilities that affect them.
OSV-Scanner supports a wide range of project types, package managers and features, including but not limited to:
- Languages: C/C++, Dart, Elixir, Go, Java, Javascript, PHP, Python, R, Ruby, Rust.
- Package Managers: npm, pip, yarn, maven, go modules, cargo, gem, composer, nuget and others.
- Operating Systems: Detects vulnerabilities in OS packages on Linux systems.
- Containers: Scans container images for vulnerabilities in their base images and included packages.
- Guided Remediation: Provides recommendations for package version upgrades based on criteria such as dependency depth, minimum severity, fix strategy, and return on investment.
OSV-Scanner uses the extensible OSV-Scalibr library under the hood to provide this functionality. If a language or package manager is not supported currently, please file a feature request.
The underlying database, OSV.dev has several benefits in comparison with closed source advisory databases and scanners:
- Covering most open source language and OS ecosystems (including Git), it’s comprehensive.
- Each advisory comes from an open and authoritative source (e.g. GitHub Security Advisories, RustSec Advisory Database, Ubuntu security notices)
- Anyone can suggest improvements to advisories, resulting in a very high quality database.
- The OSV format unambiguously stores information about affected versions in a machine-readable format that precisely maps onto a developer’s list of packages
The above all results in accurate and actionable vulnerability notifications, which reduces the time needed to resolve them. Check out OSV.dev for more details!
To install OSV-Scanner, please refer to the installation section of our documentation. OSV-Scanner releases can be found on the releases page of the GitHub repository. The recommended method is to download a prebuilt binary for your platform. Alternatively, you can use
go install github.com/google/osv-scanner/v2/cmd/osv-scanner@latest to build it from source.
For more information, please read our detailed documentation to learn how to use OSV-Scanner. For detailed information about each feature, click their titles in this README.
Please note: These are the instructions for the latest OSV-Scanner V2 beta. If you are using V1, checkout the V1 README and documentation instead.
osv-scanner scan source -r /path/to/your/dir
This command will recursively scan the specified directory for any supported package files, such as package.json, go.mod, pom.xml, etc. and output any discovered vulnerabilities.
OSV-Scanner has the option of using call analysis to determine if a vulnerable function is actually being used in the project, resulting in fewer false positives, and actionable alerts.
OSV-Scanner can also detect vendored C/C++ code for vulnerability scanning. See here for details.
OSV-Scanner supports 11+ language ecosystems and 19+ lockfile types. To check if your ecosystem is covered, please check out our detailed documentation.
OSV-Scanner also supports comprehensive, layer-aware scanning for container images to detect vulnerabilities the following operating system packages and language-specific dependencies.
| Distro Support | Language Artifacts Support |
|---|---|
| Alpine OS | Go |
| Debian | Java |
| Ubuntu | Node |
| Python |
See the full documentation for details on support.
Usage:
$ osv-scanner scan image my-image-name:tag
License Scanning (Experimental)
Check your dependencies' licenses using deps.dev data. For a summary:
osv-scanner --experimental-licenses-summary path/to/repository
To check against an allowed license list (SPDX format):
osv-scanner --experimental-licenses="MIT,Apache-2.0" path/to/directory
Offline Scanning (Experimental)
Scan your project against a local OSV database. No network connection is required after the initial database download. The database can also be manually downloaded.
osv-scanner --experimental-offline --experimental-download-offline-databases ./path/to/your/dir
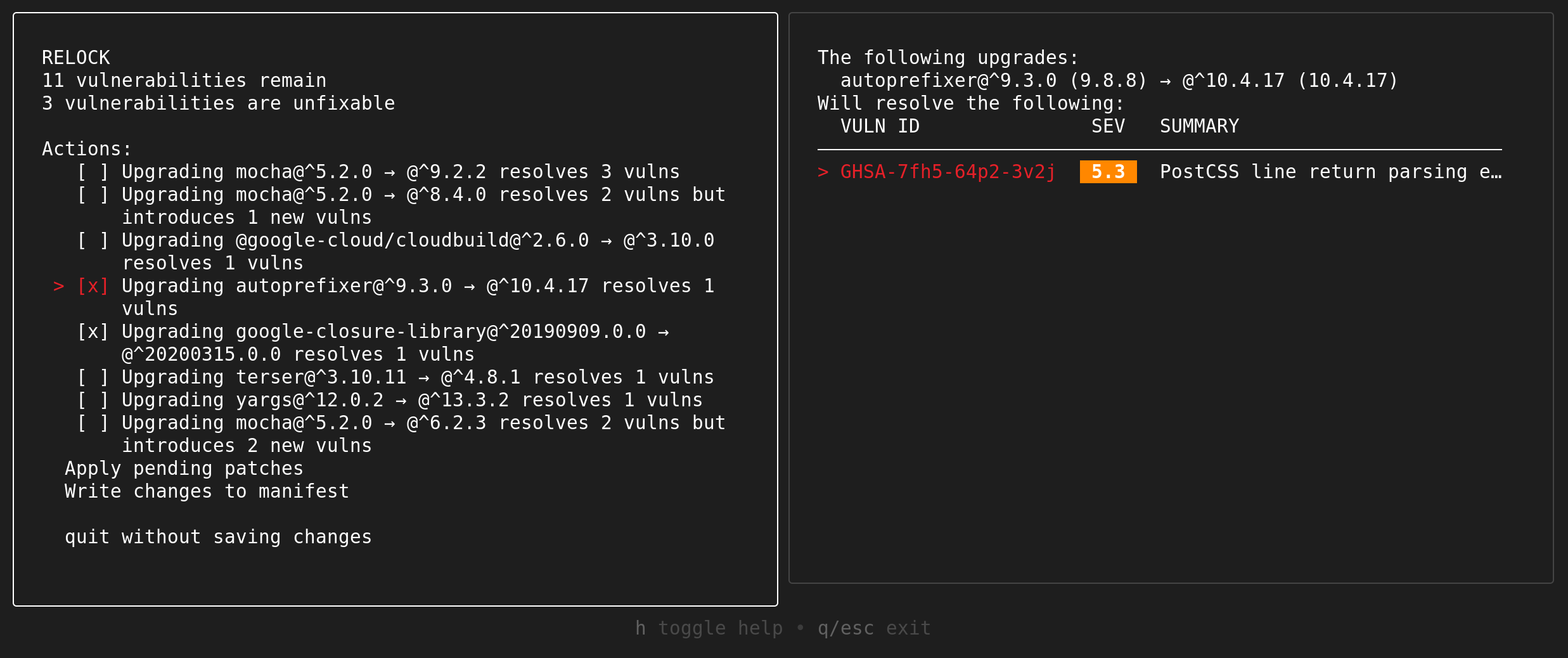
Guided Remediation (Experimental)
OSV-Scanner provides guided remediation, a feature that suggests package version upgrades based on criteria such as dependency depth, minimum severity, fix strategy, and return on investment. We currently support remediating vulnerabilities in the following files:
| Ecosystem | File Format (Type) | Supported Remediation Strategies |
|---|---|---|
| npm | package-lock.json (lockfile) |
in-place |
| npm | package.json (manifest) |
relock |
| Maven | pom.xml (manifest) |
override |
This is available as a headless CLI command, as well as an interactive mode.
$ osv-scanner fix \--max-depth=3 \--min-severity=5 \--ignore-dev \--non-interactive \--strategy=in-place \-L path/to/package-lock.json
$ osv-scanner fix -M path/to/package.json -L path/to/package-lock.json
If you have what looks like a bug, please use the GitHub issue tracking system. Before you file an issue, please search existing issues to see if your issue is already covered.
See CONTRIBUTING.md for documentation on how to contribute code.